NIST Compliance: Reporting Automation Benefits

Automating NIST compliance reporting saves time, reduces costs, and improves accuracy. Manual methods are slow, error-prone, and expensive, often taking 12–18 months and costing $250,000–$500,000. Automation tools streamline evidence collection, provide real-time monitoring, and ensure continuous compliance with frameworks like NIST 800-53 and CSF 2.0. Key benefits include:
- Improved Accuracy: Tools integrate with existing systems, reducing human errors and mapping data directly to compliance controls.
- Time & Cost Savings: Automation can cut compliance efforts by 50–70%, reducing audit preparation time and staff workload.
- Continuous Monitoring: Real-time alerts for misconfigurations help address issues before audits or breaches occur.
Organizations like Adyton and Hylan Group have successfully implemented automation, achieving faster compliance, better security, and significant resource savings. Transitioning to automation involves selecting the right tools, integrating them with current systems, and training staff effectively.
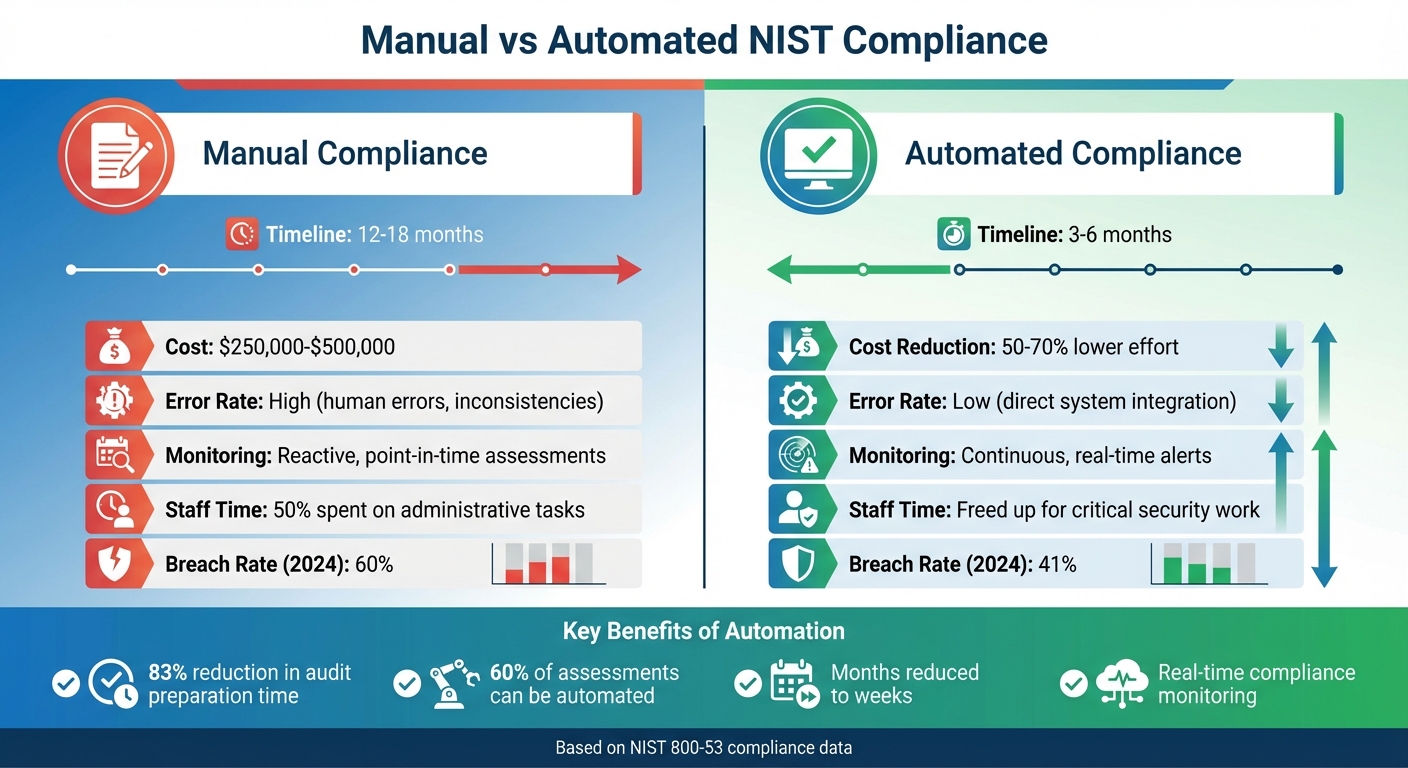
Manual vs Automated NIST Compliance: Time, Cost, and Efficiency Comparison
Benefits of Automating NIST Incident Reporting
Better Reporting Accuracy
Automation tools seamlessly integrate with your existing tech stack, pulling in logs, configuration data, and access records automatically. This eliminates the errors and inconsistencies that often come with manual tracking efforts. Plus, the evidence collected is mapped directly to NIST 800-53 controls, ensuring it aligns with regulatory requirements.
Security Automation and Orchestration (SAO) tools take this further by aggregating and correlating event data from multiple sources, which improves overall reporting accuracy. As Katie Bykowski from Swimlane puts it:
SAO can automate the analysis process, saving time and making team members more productive... [it] can also automate the steps required for aggregation and correlation from multiple sources.
This automation provides a clearer picture of attack methods and targets compared to manual processes. Predefined playbooks ensure incident data is consistently captured and reported, reducing the risk of compliance issues. The result? More accurate reporting that saves both time and resources.
Reduced Time and Resource Requirements
One of the biggest advantages of automation is the time it saves. Achieving NIST 800-53 compliance manually can take 12 to 18 months and cost anywhere from $250,000 to $500,000. With automation, organizations can start seeing progress in as little as 3 to 6 months. In fact, automation can cut compliance efforts by 50% to 70%.
Security teams often spend up to half their time on administrative tasks - time that automation can free up for more critical security work. Automated evidence collection alone can save hundreds of hours during each audit cycle. Gordon Young, Lead InfoSec Analyst at Adyton, highlights this impact:
Adyton cut compliance-related effort by 50-70%, eliminating the need to hire additional compliance personnel and ensuring continuous monitoring without the burden of manual processes.
By automating these processes, compliance shifts from being a labor-intensive, periodic task to an ongoing, streamlined effort.
Continuous Compliance Monitoring
Automation doesn’t just improve accuracy and efficiency - it enables continuous compliance monitoring. Unlike traditional manual methods, which are often reactive, automation turns NIST compliance into a proactive, ongoing process. Automated platforms monitor system configurations and security settings in real time, alerting teams immediately if compliance drift or misconfigurations occur. This allows organizations to address vulnerabilities before they become audit findings.
Real-time dashboards consolidate compliance data into a single view across both cloud and on-premises environments, eliminating blind spots caused by "shadow IT". These systems continuously collect evidence - such as logs and access records - through direct integrations with your existing tools. The impact is clear: organizations using automated Governance, Risk, and Compliance (GRC) tools had a 41% breach rate in 2024, compared to 60% for those managing risk manually. As Fortinet explains:
When compliance processes are automated, the only role a human may have to play is reacting to accurate alerts and updating the system when regulations are adjusted.
How to Implement Reporting Automation for NIST Compliance
Selecting Automation Tools
Before diving into automation, start by identifying your organization’s specific needs. The tool you choose should support the full range of NIST 800-53 controls - low, moderate, and high baselines - and allow for cross-mapping to frameworks like CMMC, FedRAMP, and NIST 800-171. This "collect once, apply many" strategy helps reduce repetitive tasks across overlapping compliance requirements.
Integration is another critical factor. The automation platform should work seamlessly with your existing tech stack, such as cloud platforms like AWS or Azure, identity management systems, endpoint security tools, and SIEM solutions. These integrations enable the tool to automatically pull real-time security metrics. Look for features like AI-powered risk identification and mitigation recommendations to streamline processes further.
It's also important to pinpoint your pain points, whether they involve evidence collection, managing vendor risks, or manual data entry. Make sure the platform includes access to compliance experts or former auditors to guide you through more complex assessments.
Once you’ve selected the right tool, connect it to your systems to maximize its efficiency.
Connecting Automation with Current Systems
Adopt a "check-remediate-validate" pattern to integrate automation with your existing systems. This approach ensures continuous monitoring, as outlined by Nawaz Dhandala:
Compliance automation... turns manual audit checklists into executable code
and
ensures continuous compliance rather than point-in-time assessments.
Streamline processes by mapping NIST controls to automation playbooks. For instance, link access control requirements to SSH configuration checks or encryption standards to TLS certificate validation. Incorporate these playbooks into your CI/CD pipelines with tools like GitHub Actions, so compliance checks run automatically whenever infrastructure code is updated. Use system schedulers, such as cron jobs or systemd timers, to perform regular compliance scans instead of waiting for annual audits.
In DevSecOps environments, Policy-as-Code tools like CloudFormation Guard or CDK-Nag can be particularly helpful. These tools catch non-compliance issues - such as public S3 buckets or unencrypted databases - before deployment, preventing problems from reaching production. Start by automating high-risk areas and gradually expand automation across your entire compliance framework.
Staff Training and Tool Adoption
Once the tools are integrated, the focus shifts to training your team. Design training programs tailored to different technical roles, distinguishing between privileged and non-privileged users. This ensures everyone understands their responsibilities within the automated system and helps ease the transition from manual to automated processes.
Management support is key here. Leadership should back the automation policy and document this commitment in Standard Operating Procedures (SOPs). These SOPs should clearly define how users and system operators interact with the tools.
As Fortinet highlights:
effective training ensures team members are given the pertinent security controls training, including how these controls protect their systems.
A good starting point is to give compliance teams read-only access to real-time monitoring dashboards. This allows them to see the benefits of automation without risking accidental changes. Use automated notifications, like Amazon SNS emails, to integrate compliance updates into existing workflows. Finally, set up feedback loops through informal workshops where staff can share experiences and collaborate directly with tool developers. This fosters continuous improvement and better adoption of the new tools.
Case Studies and Applications
Case Study: Faster Incident Reporting
These real-world examples show how automation can revolutionize incident reporting for NIST compliance. They highlight the practical benefits of improved accuracy and efficiency that automation brings.
Take the case of a leading credit union in the financial services sector. This organization failed a compliance audit because it relied on Microsoft Excel spreadsheets to manually track security policies across a multi-vendor environment, including Palo Alto and Check Point firewalls. This manual process left gaps in security policy visibility.
After switching to FireMon's automated policy management platform, integrated with ServiceNow, the credit union achieved full NIST and PCI compliance. Even better, they slashed audit preparation time by 83%. Reflecting on this shift, the Director of InfoSec shared:
A failed audit told us otherwise. I wish we went with FireMon earlier as the time and manpower savings have been incredible.
Another compelling example comes from the infrastructure sector. Hylan Group automated the enforcement of NIST 800-63b password standards across eight domain controllers in just one hour. By eliminating mandatory periodic password resets and implementing NIST guidelines, the company significantly improved enterprise security. Ramon Diaz, Director of IT at Hylan, noted:
This project allowed us to improve enterprise security and reduce helpdesk resources dedicated to passwords by 90%.
Additionally, this automation freed up 20–30% of IT staff time, allowing them to focus on other critical business initiatives.
Implementation Lessons
These examples highlight important lessons for implementing automation effectively. Relying on manual, spreadsheet-based tracking can create a misleading sense of compliance that often gets exposed during audits - a costly and reactive approach.
Both organizations avoided overhauling their entire infrastructure. Instead, they integrated automation tools into their existing systems - ServiceNow for the credit union and Active Directory for Hylan. This approach minimized disruptions while delivering significant efficiency gains, proving that automation works best when it enhances existing workflows rather than replacing them entirely.
6clicks expert guide - Automating NIST Cybersecurity Framework compliance with 6clicks
Conclusion: Automation's Impact on NIST Compliance
Automation transforms NIST compliance from a slow, reactive process into an ongoing and efficient operation. Michaela Iorga, Senior Technical Lead at NIST, highlights this shift:
Our internal estimates indicate that months of assessment efforts can be reduced to weeks, with additional benefits and enhanced security understanding of the systems assessed.
The advantages go well beyond saving time. For example, defense tech firm Adyton reported cutting compliance efforts by an impressive 50–70% through automation.
In addition to efficiency, automation improves accuracy and consistency. By leveraging machine-readable formats like OSCAL, around 60% of assessments can be automated, resulting in reliable and consistent outcomes. This streamlined approach frees up security teams to focus on critical, high-priority tasks instead of repetitive documentation.
FAQs
What should we automate first for NIST reporting?
The initial step in automating NIST reporting is focusing on continuous monitoring and evidence collection for security controls. By automating these processes, you can simplify workflows, maintain efficiency, and ensure your organization stays compliant with NIST standards over time.
How do we prove automated evidence is audit-ready?
To make sure automated evidence meets audit standards, organizations need to confirm that records are accurate, complete, unalterable, and easily accessible. Automated systems should maintain consistent, timestamped logs that align with regulatory guidelines. This not only simplifies report generation but also helps ensure compliance with audit requirements.
How long does NIST reporting automation take to roll out?
The time it takes to implement NIST reporting automation varies based on an organization's size and complexity. That said, the system is built for quick deployment, allowing businesses to maintain ongoing compliance without extended interruptions.